Invisible to Threats.
Visible to You.
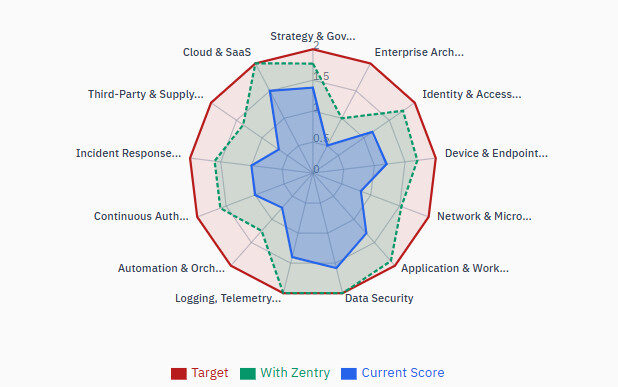
Your most critical assets sit at the edge of your network, and right now, they're visible to anyone looking. Open ports. Static IPs. Traditional method dependencies. Every one of them is an invitation. The Zentry solution changes the equation entirely. By embedding zero trust directly into the hardware and eliminating inbound attack surfaces at the device level, Zentry zero trust makes your industrial network invisible to threats while giving you complete visibility and control over every connection, every user, and every device.
No exposure. No compromise. No exceptions.
The FreeWave Zentry secure connectivity offer is designed for leaders in manufacturing, industrial operations, and enterprise IT. Whether you’re securing a factory floor, managing distributed assets, or protecting sensitive corporate data, the Zentry solution scales to meet your needs.
Available embedded on the FreeWave Elements™ ES1000 or as a standalone solution, Zentry security can provide ubiquitous protection to assets wherever they are located. It offers:
Invisible Attack Surface
No public IPs, open ports, or static tunnels to scan or exploit.
Built for Enterprise and the Edge
Works seamlessly across OT, IoT, and in disconnected environments where most Zero Trust tools cannot operate.
Simple Integration
Installs in minutes and works alongside existing SOC, SIEM, and firewall tools without complex reconfiguration.
Ephemeral sessions
Access appears only when needed and disappears when complete, leaving no standing exposure
No False Positives
Deterministic control removes noise, helping small security teams focus on real threats.
Identity-driven access
Ties every connection to a verified user, device, and policy for precise control.
Disclaimer: the information provided in the assessment is for informational purposes only. FreeWave does not guarantee results based on this assessment, alone.*Eligibility is limited.
Don't believe it? Take the Zentry Workshop, now and see where your risk is and how we can reduce it.
Take 30 minutes to take the Zentry assessment and receive an in-depth look at your own network vulnerabilities and how integrating the Zentry solution can close them.
Click here to take the challenge, now.