“You must remember … as many times as we win, the bad guys only get better. Our battles are just beginning!”
These words conclude a graphic novel by Dr. Chase Cunningham and coauthor Heather Dahl. In “The Cynja: Volume 1,” the protagonist is the evil Botmaster. His thick, purple tentacles; sharp, black claws; and digital-looking scythe try to take down networks in the time it takes to turn the page.
The concept is scary real.
We sat down with Cunningham for our blog, “Stranger than Fiction: Exploring the New Battlefield at the Industrial Edge with Chase Cunningham (Part 1),” where we explored the rise of cyber threats on the industrial edge and why turning things on, crossing your fingers, and hoping your network stays safe is antiquated and risky.
Cunningham, a former U.S. Navy officer who worked in cryptology with National Security Agency and Forrester street cred, now consults with international companies and public organizations. His military experience taught him two things.
First, small businesses are targets for nation states because of their connective links to other things (the nature of technology is that attackers get past defenses and sprawl; it’s the difference between a break-in and a break-in-and-move-into-every-room scenario).
Second, if you fail to plan, you plan to fail, underscoring Cunningham’s favorite wrong to right. He maintains that operational leaders should remove trust inside the network, first and foremost.
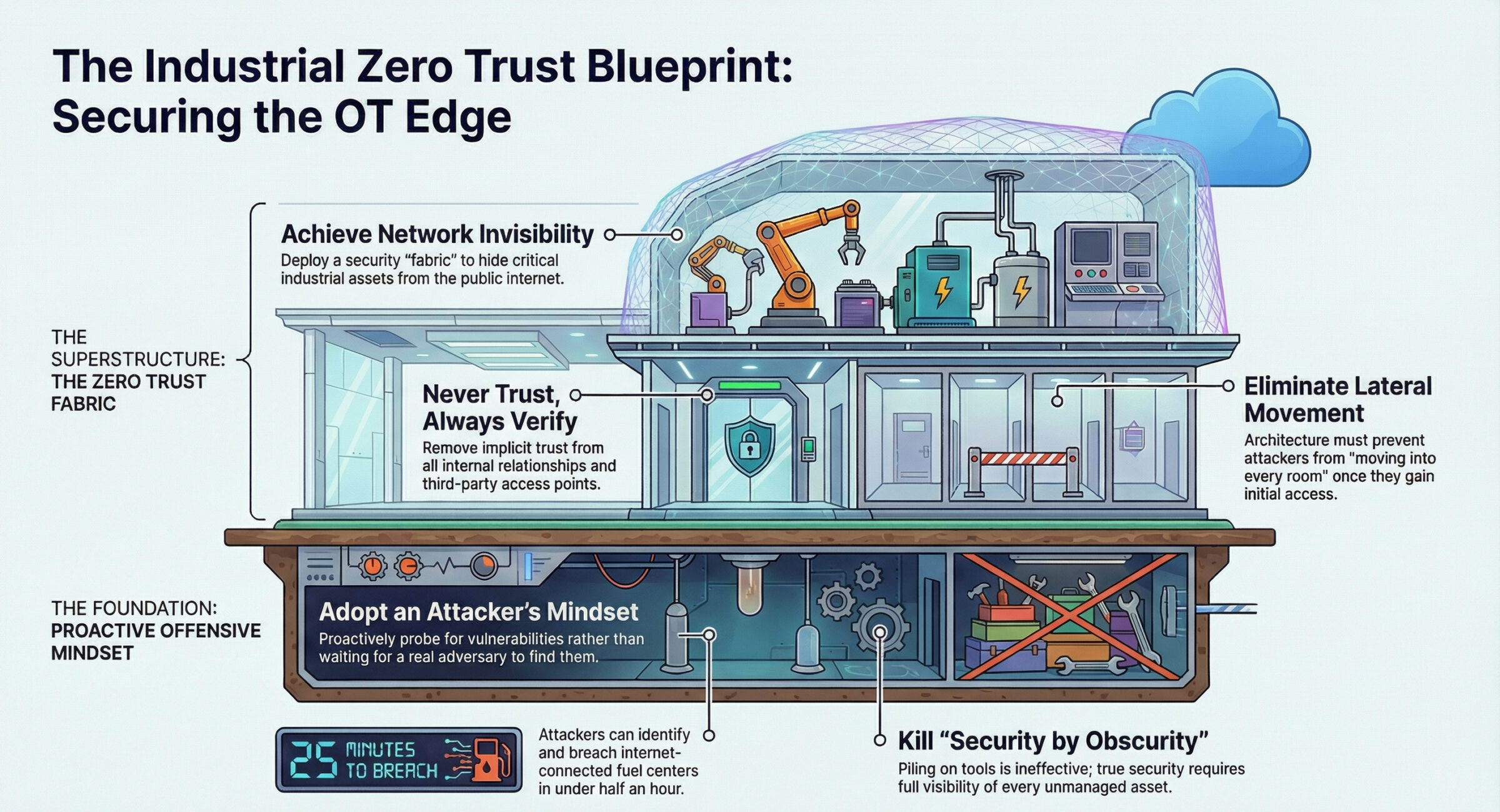
Here, we give you three essentials for your network security strategy at the industrial edge, directly from Dr. Zero Trust himself.
Essential #1: Offense Wins
For OT (operational technology) leaders seeking to protect edge infrastructure, an offensive strategy increases your odds of staying secure. Dramatically.
Cunningham’s perspective is clear: the advantage belongs to those who think like attackers.
“Are you willing to engage in a red team operation … and let a group of hackers essentially come at you and tell you where you’ve got vulnerabilities?” If the answer is no, then he says there’s an issue right there. For Cunningham, an offense-minded strategy starts with confronting reality and actively probing for security weaknesses the same way an adversary would.
That mindset is critical because, in his words, “how can you possibly defend what you don’t know about?” Industrial environments are often sprawling, with unseen or unmanaged assets. Without full visibility, attackers will exploit your most vulnerable gaps first.
He frames out the risk in real time. “I could breach these folks in about 25 minutes.” The “folks” Cunningham refers to are fuel centers talking to the internet that he has, with a few clicks, identified. Even more concerning, “a lot of these have crappy usernames and passwords like admin passwords. I could go in there and change fuel controls.”
The takeaway isn’t theoretical. Attackers win because they take direct, simple paths into exposed systems. Organizations that take a defensive stance, he says, don’t test potential paths themselves. Instead, they wait for an attacker to do it for them.
Cunningham is equally blunt about why traditional approaches fail. “Security by obscurity is not going to keep you safe.” Piling on tools doesn’t solve it either. “If the dart board is continuously moving,” he says, “the odds of me hitting that bullseye is pretty slim.” Reactive defense cannot keep pace with adaptive threats.
“Getting breached is not the big problem,” Cunningham adds. “Someone will find a way to get past whatever defense you’re putting in front of them.” If compromise is inevitable, then success depends on how quickly you detect, isolate, and respond. These safeguards come from understanding how attacks actually unfold.
In industrial operations, offense wins. Organizations that continuously test, expose, and reduce vulnerabilities don’t wait for a real attacker to do it for them.
Essential #2: Zero Trust Protects the Entire Network
Dark actors target ICS (industrial control systems) and OT environments. Why? As mentioned in part 1 of this series, industrial infrastructure has evolved rapidly with many more entry points because of today’s ultra-connected world. The cloud, internet and mobile workforce have expanded the attack surface. As a result, attackers don’t look for targets, they look for vulnerabilities. No one is too small or too big.
Successful network security strategy means moving beyond legacy perimeter security to dynamic, zero-trust strategies governed by “never trust, always verify.” The goal is to protect the entire network and build resilience against evolving threats so disruptions are eliminated.
“A lot of people have been burned without a clear ROI,” Cunningham says. “There’s a unique space around IoT, IT/OT and binary-type applications. OT devices are only supposed to do one or two things and pull up data. The OT space fits well into the strategic side of the equation.” Understanding and knowing what’s going on with your devices is a good start.
To Cunningham, security is much bigger than one organization. After leaving the NSA he was assigned a project around zero trust that was already underway at Forrester. He quickly realized that if he was a bad guy, zero trust would have made his life miserable. His thinking around security quickly changed.
“I built a framework. I have kids. I really think that in a world where everyone is digital and in a space where we have … access to the internet and all these other things, operating securely is a fundamental human right.”
Essential #3: Make Your Network Invisible Through a Zero Trust Mindset
Attackers can’t exploit a network they cannot see. Yet, according to Cunningham, there’s a critical step before you get to actual technology tools: embracing a zero-trust mindset so people inside your organization become, well, skeptics.
Zero trust is not a single product or model, but a mindset that removes implicit trust from all relationships inside your network.
Start with the basics.
- Define maximum control. What control do you have right now? Where are the gaps?
- Minimize lateral movement. Do third-parties have access? Does your security allow people to move around easily within your network once they are in?
- Don’t empower adversaries. Are you thinking offensively? What moves by an attacker can you anticipate?
Cunningham says, “If they (companies) don’t have dedicated teams, security is a big deal. People think ‘I can’t do it myself.’ This is security by obscurity.” He likens cyberspace with the Serengeti where the gazelle must always be on high alert, ready to outsmart the lions.
One big mistake, he says, is thinking that buying the right tech tools and applying the right controls will solve the problem, but that is like throwing “a million darts at the wall while the wall is moving. It’s slim to hit the bullseye.”
A better way to think? Choose network security that makes your network invisible.
Good News: Network Security Problems Are Solvable
Cunningham emphasizes that the risks are real, but so are the solutions. Focus on what you can control, and contribute to the broader security ecosystem by securing your own environment with intention, strategy, and purpose. One solution Dr. Zero Trust has pen tested with impressive results is the FreeWave Zentry™ solution, a zero-trust-based solution that protects critical industrial assets by design.
The security software acts as a security “fabric” overlaid onto OT systems, without ripping and replacing equipment. It makes the network virtually invisible. The Zentry solution can be deployed on its own or complement the FreeWave Elements ES1000™, a cellular gateway powered by zero trust.
Cunningham says that in OT, there’s great value in having a physical box that can be put anywhere it needs to go with software taking care of the rest. ”FreeWave’s done a good job of putting together an OT solution for bridging the gap where folks want to be met,” he says. “That ability to be flexible in the delivery to customers is useful.”
In the age of AI and quantum computing, it’s the right time to prioritize security for OT leaders.
Modern network security aligns all three of the essentials outlined here. Thinking like an attacker positions you on offense, the place you want to be to win. Architect for resilience with zero trust to protect against lateral movement, a path to devastating outcomes like downtime and lost revenue. Eliminate exposure altogether with a zero- trust mindset by making your network invisible.
When these three essentials work together, you’re upping your odds in creating a winning network security strategy.
Take the Zentry workshop challenge and explore your network invisibility with FreeWave Zentry.



