
In today’s world, every CEO, CIO, CSO, or CFO is liable for compliance and failing “Pen Testing” (penetration testing) scores, not to mention rising insurance premiums. The pressure of thwarting the increasing security breaches and hacks demand a robust solution that lowers costs and increases network security without navigating complex solutions from multiple vendors.
So what is the value proposition of adding security to an OEM’s device early in the product life cycle?
“If you were just offering a communications device before, you could be looking at increased network security through the same lens as everyone else,” said Michael Tate, chief operating officer and senior vice president of global sales and marketing for FreeWave. He adds, “The outcomes transform commodity-priced hardware into a differentiated solution.”
“Today you are selling hardware and tomorrow you are selling a valuable solution with ARR, all while becoming more relevant to your customer and solving real security problems over just connectivity. If you have devices that give you security and also include communications, you’re going to win faster.”
“If you have devices that give you security and also include communications, you’re going to win faster.” - Michael Tate, chief operating officer and senior vice president of global sales and marketing for FreeWave
For OEMs, proactive threat detection starts with zero trust. Zero trust ensures every interaction is verified and that OEM products are trustworthy.
OEMs and Preparing for the Future
The importance of cybersecurity extends to our readiness as a nation. Thousands of OEMs contribute to the U.S. defense industrial supply chain across 16 critical infrastructure sectors. According to the U.S. Department of Defense Cybersecurity Strategy, the first of its kind in the country’s history, ensuring our safety means having “a cybersecurity framework built upon zero trust principles.”
As a network is continuously monitored, a zero trust security approach gives systems administrators time to focus on highest-risk items and stay ahead of threats. The Department of Defense has committed to fully deploy zero trust by the end of 2027.
The demands for OEMs to address security are rapidly evolving. Secure by Design is a principle that prioritizes security early in design rather than leaving it as an afterthought. 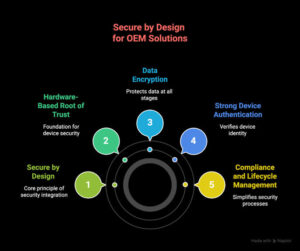
Industrial sectors like oil and gas, energy, municipal water, and wastewater departments use thousands of devices across a network. These assets have multiple contracts and multiple vendors. A disgruntled employee or third-party vendor has the potential of seeing everything and doing serious damage with traditional security. Yet, a minute of downtime can cost millions.
Take North America’s largest steel producer, $30 billion Nucor, as an example. Its data breach in May 2025 due to “unauthorized third-party access” triggered shutdowns at multiple facilities.
As IT/OT integration grows, the Nucor data breach underscores how cyberattacks are growing in sophistication right along with the attack surface, which includes IIoT devices, communications, gateways, sensors, robotics, industrial routers, PLCs, and wireless access points.
Security, it turns out, is everyone’s concern, especially forward-thinking OEMs of industrial-grade networking hardware and edge devices like cellular routers, gateways, and modems. Secure by Design products give OEMs differentiation in a crowded marketplace.
FreeWave Offers OEMs Competitive Advantage
FreeWave has committed more than 30 years to developing industrial wireless solutions. Today, its end-to-end IIoT solutions transform connectivity, security, edge intelligence, and data insights for remote industrial enterprises around the world.
OEMs with small, niche markets to mass-produced industrial-grade products successfully embed FreeWave solutions in agricultural products, automation technology and edge devices.
The FreeWave Zentry™ solution is a zero-trust based security solution. It cloaks protected networks, making them “invisible” utilizing a simple concept: never trust, always verify. This means the system doesn’t automatically trust anyone or anything trying to connect to it – even if they’re coming from inside the network. Instead, every access request attempting to access resources is verified whether from a user, device, or application, no matter where they are.
Here are seven reasons OEMs are addressing security early in the product development life cycle and how the Zentry solution impacts outcomes for both OEMs and their customers.
- Differentiation in a Commodity Market
The Zentry solution allows OEMs to stand out by embedding advanced network security directly into their products, moving them beyond commodity hardware and giving them a unique selling proposition. This makes their offerings more relevant and valuable to customers, helping them pull away from competitors who only provide standard connectivity features. - Simplified and Consolidated Security
By integrating the Zentry solution, OEMs offer consolidated network security as part of their product, eliminating the need for customers to manage separate VPNs, static IPs, port forwarding, and multiple vendors. This reduces complexity, points of failure, and administrative overhead for OEMs and their end customers. - Increased Network Security
The Zentry solution provides a zero-trust overlay, making devices and networks “invisible” to unauthorized users. It encrypts communications, limits access strictly to what’s needed, and reduces the attack surface – key for critical infrastructure and remote assets. This is especially valuable as cyber threats and ransomware attacks increase across industries. - Improved ROI and Lower Total Cost of Ownership
With the Zentry solution, OEMs and their customers reduce costs by eliminating unnecessary hardware, software, and ongoing maintenance. The solution is aggressively priced, easy to deploy (setup in minutes), and intuitive to manage, making it accessible even for organizations with limited IT resources. - Flexibility and Broad Compatibility
The Zentry solution can be installed on any device with a Linux environment, including cellular gateways, inexpensive Linux boxes, laptops, tablets, and servers, making it broadly compatible with existing OEM hardware and easy to integrate into diverse product lines. - Multi-Tenant Management and Scalability
The Zentry console is multi-tenant, allowing OEMs to manage security for their own products and for their customers, supporting SaaS and managed service models. This enables new revenue streams and value-added services. - Future-Proofing and Market Relevance
As security becomes a top priority for buyers, OEMs embedding the Zentry solution are better positioned for the future, offering solutions that address both current and emerging threats, and aligning with the industry’s shift toward integrated, secure, and intelligent edge devices.




