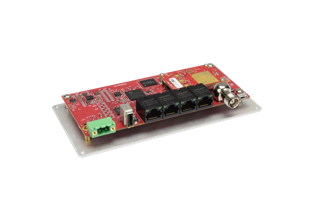
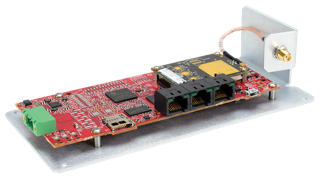
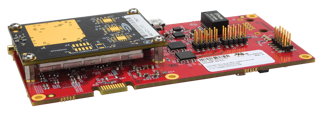
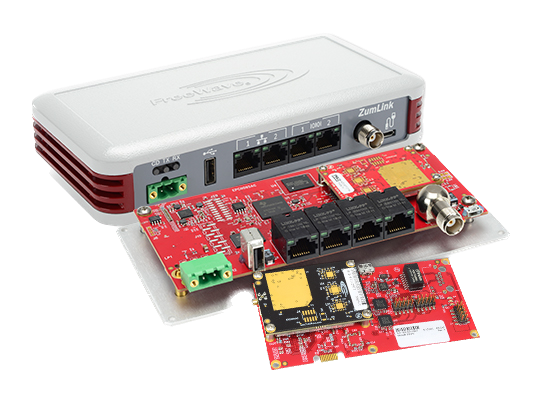
ZumLink™ Future-Ready Industrial Radio
Rugged 900 MHz Ethernet Radio Series
FreeWave’s ZumLink™ 900 Series is made for secure collection, transport, and control of data in rugged industrial environments. These radios provide a long-range, low-power solution for remote wireless communications—with capabilities that can be seamlessly added as IIoT requirements evolve.
In fact, the ZumLink 900 Series is software upgradable to include FreeWave’s IQ Application Environment, a Linux-based platform to deploy and run third-party industrial applications.
ZumLink Future-Ready Industrial Radio
Rugged 900 MHz Ethernet Radio Series
FreeWave’s ZumLink 900 Series is made for secure collection, transport, and control of data in rugged industrial environments. These radios provide a long-range, low-power solution for remote wireless communications—with capabilities that can be seamlessly added as IIoT requirements evolve.
In fact, the ZumLink 900 Series is software upgradable to include FreeWave’s IQ Application Environment, a Linux-based platform to deploy and run third-party industrial applications.
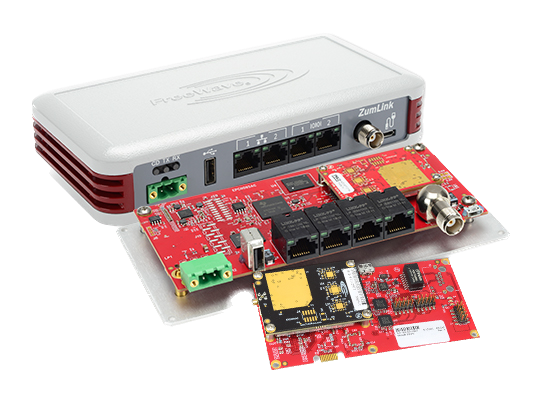
Key Features
-
Unlicensed 900 MHz Spectrum
Cost effective, easy to deploy
-
High-Speed Data Rates
Five RF link rates supporting from 80 kbps to 4 Mbps
-
Long Range
Up to 97 km (60 miles) with clear line of sight
-
Leverages FreeWave’s Network Accelerators
Packet Compression, packet aggregation, forward error correction, and adaptive spectrum learning to maximize network efficiency
-
Low Power
355 mA @ 12V in transmit; 145 mA @ 12V in receive
-
Secure
Frequency Hopping Spread Spectrum (FHSS) technology; SSH, SNMP, 128-bit, and 256-bit AES counter mode encryption options
-
Industrial Grade
Class I, Division 2 certified; operating in temperatures from -40°C to 75°C
-
IQ-Ready
Software upgradable to include FreeWave’s IQ Application Environment, a Linux-based platform to deploy and run edge applications
All Models
Is the ZumLink right for my applications?
We’ll help you decide. See an example of these radios in use, or tell us your operational requirements so that we can recommend your best-fit solution.
Ready to get started?
See how you can rapidly evolve your edge with FreeWave’s help.